With the release of vCloud Director 10, further advances were made in the Appliance. There are now various types of configurations of the appliance that includes both application cells and DB cells (PostgreSQL). It has become more stable and I would recommend using it for any new deployments. A basic production installation consists of 3 DB cells and 3 app cells. The official VMware documentation does a fairly good job of explaining the deployment and can be found here.
In this post, I will go through the replacement of the self signed certificates on the cells. (In a previous post I explained how to deploy a Microsoft CA for use in a lab if you need one.) In this example, I will produce a single signed certificate that will server both the html 5 interface and the console proxy.
Step 1. First we are going to produce an unsigned certificate and place the, in a new certificate store. (It will be replaced with signed certificate later but we need the keys for the signing) Open a SSH session to your vCD instance and change to the /tmp directory. Execute the script below to create the certificate. It is placed in a certificate store called certificates.ks. You can ignore the warning about the JCEKS keystore using a propriety format. You should then have a file called certificates.ks in the /tmp directory.
/opt/vmware/vcloud-director/jre/bin/keytool \ -keystore certificates.ks \ -alias http \ -storepass ChangeMe \ -keypass ChangeMe \ -storetype JCEKS \ -genkeypair \ -keyalg RSA \ -keysize 2048 \ -validity 3650 \ -dname "CN=vcd-dc2-001.local, OU=VCPP Sales, O=VMware, L=Palo Alto, S=California, C=US" \ -ext "san=dns:vcd-dc2-001.local,dns:vcd-dc2-001,ip:192.168.28.81"
Step 2. Next we going to produce a certificate signing request (CSR) that we will send on to our Certificate Authority (CA). Once you execute the script below, you should end up with a new file called vcd-dc1-001-http.csr
/opt/vmware/vcloud-director/jre/bin/keytool -keystore certificates.ks \ -storetype JCEKS \ -storepass ChangeMe \ -certreq \ -alias http \ -file vcd-dc2-001-http.csr \ -ext "san=dns:vcd-dc2-001.local,dns:vcd-dc2-001,ip:192.168.28.81"
Step 3. From here we need to get the CSR signed by our CA. See Part 2 of this series to find out how. The output of that process will be a .cer file that contain the signed certificate. Make sure you also get a copy of the CA’s root certificate as you will need it in Step 4. See Part 1 of this series to get the CA Root certificate if you don’t already have it.
Step 4. We are now going to take the two .cer files collected in step 3 and load them into the certificate store file certificates.ks. You will need to use a tool like WinSCP to transfer the files to your vCD server. Once you have them there, execute the next two scripts to get the files into the store.
/opt/vmware/vcloud-director/jre/bin/keytool -keystore certificates.ks \ -storetype JCEKS \ -storepass ChangeMe \ -import \ -alias root \ -file LabCA.cer
/opt/vmware/vcloud-director/jre/bin/keytool -keystore certificates.ks \ -storetype JCEKS \ -storepass ChangeMe \ -import \ -alias http \ -file vcd-dc2-001-http.cer
Step 5. As I mentioned before, we are going to use a single certificate for both the html 5 server and the console proxy. The cell management tool is expecting two certificates with the alias http and consoleproxy. In order to make the tool work, duplicate the certificate with the http alias into and alias called consoleproxy using the scrpt below.
/opt/vmware/vcloud-director/jre/bin/keytool -keystore certificates.ks \ -storetype JCEKS \ -keyclone \ -alias http \ -dest consoleproxy \ -keypass ChangeMe \ -new ChangeMe \ -storepass ChangeMe
Step 6. Once this is done, list the contents of the certificate store to make sure all the bits are in there.
/opt/vmware/vcloud-director/jre/bin/keytool -storetype JCEKS -storepass ChangeMe -keystore certificates.ks -list

Step 7. Next, copy the certificate store to the transfer location in preparation for installing them into vCD.
cp certificates.ks /opt/vmware/vcloud-director/data/transfer/certificates.ks chown vcloud.vcloud /opt/vmware/vcloud-director/data/transfer/certificates.ks
Step 8. We going to use the cell management tool to import the certificates into vCD.
/opt/vmware/vcloud-director/bin/cell-management-tool certificates -j -p \ --keystore /opt/vmware/vcloud-director/data/transfer/certificates.ks \ --keystore-password ChangeMe
Step 9. Finally, restart the vCD service so that the new certificates are loaded and used.
service vmware-vcd restart
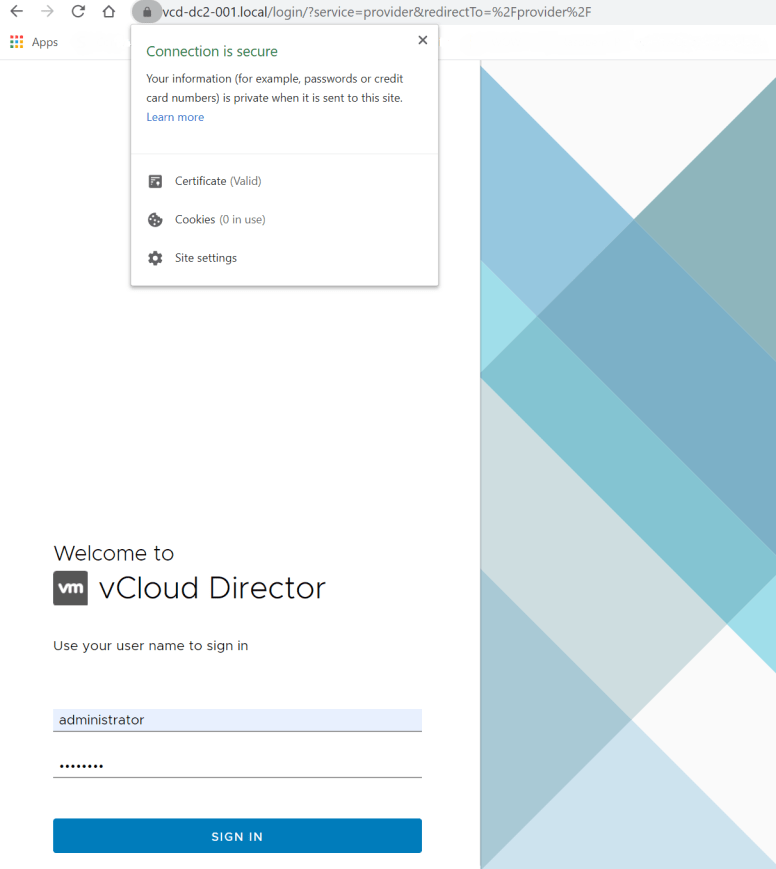
And that’s it. Give vCD a minute or two to get going and then open a new browser session to your instance. It should be nice and secure now. This will also allow you to connect through the console proxy without any issues.