Playing with vCAV and setting it up for both a lab and production environment has become considerably easier with vCAV 3.0 which is due for GA very soon. Due to the increased functionality in the solution and the ability to do a single node deployment for lab or dev environments, understanding the endpoint mappings is important. Below is a detailed look at all things networking for vCAV 3.0. (Copied from work done by
TLDR:
- Use port 443 on each appliance to do day 0 or day 2 config unless instructed otherwise.
- In dev environments and/or combined appliances, use:
- 8443 for the c4 admin UI
- 8442 for the tunnel admin UI
- 8441 for the manager admin UI
- 8440 for the replicator admin UI
- When adding local replicators, log into the manager htpps://mgr-ip:8441 and use local-rtr-ip:8043 (we almost managed to move this step in the c4 ui in 3.0, obviating the need to ever go to the manager during initial install & config, but that work was postponed and will be completed in a future release)
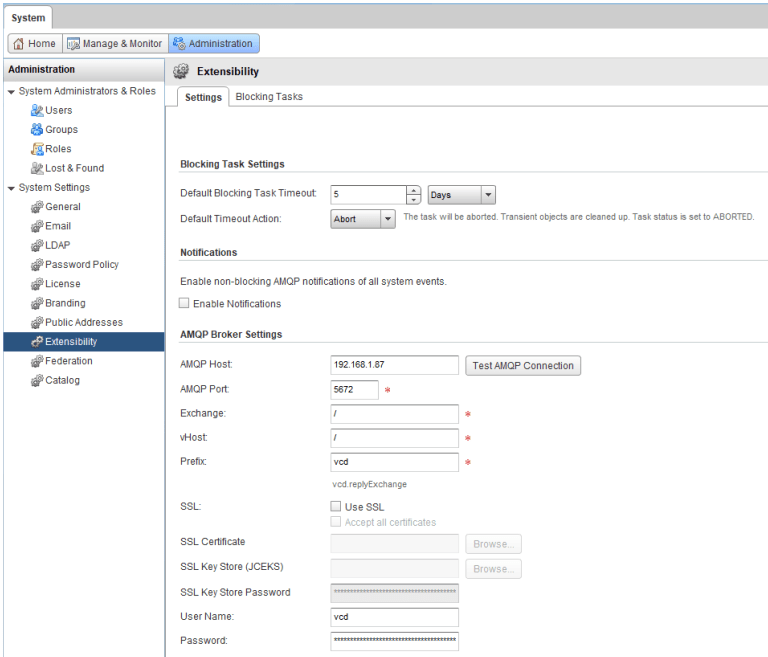
- When pairing with c4 use a hostname/literal-ip and port that lead to the tunnel data endpoint for the respective site. If you don’t have a port forwarder, or haproxy, etc (which is typically the case in dev envs), use the tunnel data endpoint directly: https://tunnel-ip:8048. Note: the public api endpoint configuration option in c4 should be explicitly set to haproxy:443 or tunnel:8048 (depending on your setup).
Services & Deployment roles
The vCAV stack consists of the following services:
- hbrsrv – low level replication data component, used by a replication at the destination site only.
- lwdproxy – adds encryption, authentication & authorization to hbrsrv, used by a replication at both the source and destination site.
- replicator – low level vCenter replication management component
- h4 manager – vCenter replication management component
- c4 – talks to vCloud Director & an h4 manager to manage and monitor vCD VM/vApp replications.
- tunnel – manages TLS tunnels across sites by running an embedded tlsnexus engine.
Deployment roles
|
Role
|
Services
|
|---|---|
| onprem | tunnel, replicator, lwdproxy, hbrsrv |
| management | c4, manager |
| replicator | replicator, lwdproxy, hbrsrv |
| tunnel | tunnel |
| combined | tunnel, c4, manager, replicator, lwdproxy, hbrsrv |
Endpoints
|
Port
|
Name
|
Deployment Roles
|
Description
|
Usage
|
|---|---|---|---|---|
| 443 | HTTPS | onprem | Iptables redirect to port 8440 (onprem replicator admin UI) | On-prem admins for installation, configuration, day2 ops of on-prem replicator |
| 443 | HTTPS | combined | Iptables redirect to port 8443 (c4 public api endpoint & portal) | Provider admins for installation, configuration, day2 ops of c4 |
| 443 | HTTPS | management | Iptables redirect to port 8443 (c4 public api endpoint & portal) | Provider admins for installation, configuration, day2 ops of c4 |
| 443 | HTTPS | replicator | Iptables redirect to port 8440 (cloud replicator admin UI) | Provider admins for installation, configuration, day2 ops of cloud replicator |
| 443 | HTTPS | tunnel | Iptables redirect to port 8442 (tunnel admin UI) | Provider admins for installation, configuration, day2 ops of cloud tunnel |
| 8043 | replicator API | onprem, replicator, combined | Replicator API port | Used by provider admin when adding local replicators. Also used internally by the h4 manager. |
| 8044 | manager API | management, combined | H4 Manager API port | Used internally by c4 and the replicators. Should never be accessed by a human operator and/or public API client for any purpose. |
| 8045 | lwdproxy API | onprem, replicator, combined | lwdproxy API port | Used internally by replicators to configure lwdproxy routes. Should never be accessed by a human operator and/or public API client for any purpose. |
| 8046 | c4 API | management, combined | C4 API port | Used internally for cross-site communication between c4 instances and cross-site communication between on-prem rtr/virgo and cloud c4. Should never be accessed by a human operator and/or public API client for any purpose. |
| 8047 | Tunnel API | onprem, tunnel, combined | Tunnel service API port | Internally by c4 (cloud side) and replicator (on-prem) for configuring the tunneling routes. Should never be accessed by a human operator and/or public API client for any purpose. |
| 8048 | Tunnel data | tunnel, combined | This is the single entry point for all ingress traffic including the UI, the public vCAV API, internal management traffic, replication data, etc. Typically, the provider will forward some-public-ip:443 to this endpoint, i.e. this endpoint is visible on the internet / remote sites. | In production, the provider will use dnat/haproxy/nsx/etc to forward port public-ip:443 to the tunnel data endpoint. Then they explicitly set the c4 public api endpoint configuration option to public-ip:443
In devel/eval use cases, there might not be a haproxy/nsx/etc to forward the traffic, and then the tunnel-addr:8048 can be set directly as the c4 public api endpoint configuration option. For this to work other c4 sites and on-prem sites must have direct connectivity to tunnel-addr:8048 (this is usually the case in test/eval environments). In any case when pairing with this cloud the on-prem admin needs to use the value that was configured in the c4 public api endpoint configuration option. |
| 8123 | hbrsrv API | replicator, onprem, combined | hbrsrv internal VMODL management API | The replicator uses this to configure hbrsrv for accepting incoming replications. Access to this port from outside of the vcav appliance should be disallowed by the appliance firewall. Should never be accessed by a human operator and/or public API client for any purpose. |
| 8440 | Replicator admin UI | replicator, combined, onprem | Should only be used by provider admins for replicator day2 operations, when the combined deployment roles is in use. | |
| 8441 | Manager admin UI | combined, management | Used by provider admins for manager install/config/day2 operations.
(In a future release we will eliminate the necessity to use this endpoint during initial setup.) |
|
| 8442 | Tunnel admin UI | combined, onprem, tunnel | Used by admins for tunnel day2 operations, when the combined deployment roles is in use. | |
| 8443 | c4 public api | combined,
management |
Should never be used by human / api users. | |
| 31031 | hbrsrv | onprem, replicator, combined | Should never be used by human / api users. | |
| 44045 | lwdproxy | onprem, replicator, combined | Should never be used by human / api users. | |
| 44046 | lwdproxy plain | onprem, replicator, combined | Should never be used by human / api users. |
FAQ
- Why do most services (tunnel, c4, manager, replicator) have two endpoints, e.g. c4 has 8443 and 8046?
– Because client certificates are used internally in the system for authentication across sites and therefore we need a TLS point that allows client certificates. However, we also need to serve the admin UIs (in the c4 case the admin UI and the tenant UI are the same thing). We cannot just serve the UIs and the internal API on the same endpoint for the following reason. Browsers will detect if a server endpoint allows client certificates and will prompt the user to select a client certificate to use for the connection, if any client certificates are installed in the browser. This is at best annoying (the user needs to ‘cancel’ the client cert prompt in the browser) or will result in notAuthenticated errors (if the user attempts to use their e-banking certificate with the vCAV services), and at worst it renders the vCD ui plugin totally unusable (unlike when visiting a site, the browser handles ajax requests differently – it rejects outright all ajax requests to a server endpoints that allow client certs, without any warning or explanation!). Therefore, we use 80XX for internal communication between components, and 844X to serve our various UIs and other API clients.